The Internet mystery that’s baffled the world: Is Cicada 3301 a puzzle, a treasure hunt or some ‘nefarious’ recruitment test?
For the past two years, a mysterious online organization has been setting the world’s finest codebreakers a series of seemingly insolvable problems. But to what end?
One evening in January last year, Joel Eriksson, a 34-year-old computer analyst from Uppsala in Sweden, was trawling the web, looking for distraction, when he came across a message on an internet forum. The message was in stark white type, against a black background.
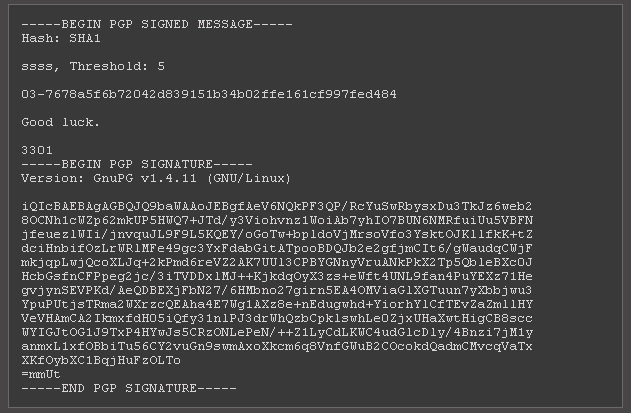
“Hello,” it said. “We are looking for highly intelligent individuals. To find them, we have devised a test. There is a message hidden in this image. Find it, and it will lead you on the road to finding us. We look forward to meeting the few that will make it all the way through. Good luck.”
The message was signed: “3301.”
A self-confessed IT security “freak” and a skilled cryptographer, Eriksson’s interest was immediately piqued. This was – he knew – an example of digital steganography: the concealment of secret information within a digital file. Most often seen in conjunction with image files, a recipient who can work out the code – for example, to alter the colour of every 100th pixel – can retrieve an entirely different image from the randomized background “noise.”
It’s a technique more commonly associated with nefarious ends, such as concealing child pornography. In 2002 it was suggested that Al-Qaeda operatives had planned the September 11 attacks via the auction site eBay, by encrypting messages inside digital photographs.
Sleepily – it was late, and he had work in the morning – Eriksson thought he’d try his luck decoding the message from “3301?. After only a few minutes work he’d got somewhere: a reference to “Tiberius Claudius Caesar” and a line of meaningless letters. Joel deduced it might be an embedded “Caesar cipher” – an encryption technique named after Julius Caesar, who used it in private correspondence. It replaces characters by a letter a certain number of positions down the alphabet. As Claudius was the fourth emperor, it suggested “four” might be important – and lo, within minutes, Eriksson found another web address buried in the image’s code.
Feeling satisfied, he clicked the link.
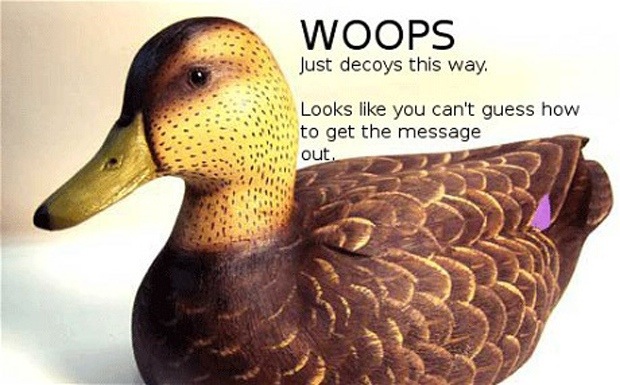
It was a picture of a duck with the message: “Woops! Just decoys this way. Looks like you can’t guess how to get the message out.”
“If something is too easy or too routine, I quickly lose interest,” says Eriksson. “But it seemed like the challenge was a bit harder than a Caesar cipher after all. I was hooked.”
Eriksson didn’t realize it then, but he was embarking on one of the internet’s most enduring puzzles; a scavenger hunt that has led thousands of competitors across the web, down telephone lines, out to several physical locations around the globe, and into unchartered areas of the “darknet”. So far, the hunt has required a knowledge of number theory, philosophy and classical music. An interest in both cyberpunk literature and the Victorian occult has also come in handy as has an understanding of Mayan numerology.
It has also featured a poem, a tuneless guitar ditty, a femme fatale called “Wind” who may, or may not, exist in real life, and a clue on a lamp post in Hawaii. Only one thing is certain: as it stands, no one is entirely sure what the challenge – known as Cicada 3301 – is all about or who is behind it. Depending on who you listen to, it’s either a mysterious secret society, a statement by a new political think tank, or an arcane recruitment drive by some quasi-military body. Which means, of course, everyone thinks it’s the CIA.
For some, it’s just a fun game, like a more complicated Sudoku; for others, it has become an obsession. Almost two years on, Eriksson is still trying to work out what it means for him. “It is, ultimately, a battle of the brains,” he says. “And I have always had a hard time resisting a challenge.”
On the night of January 5 2012, after reading the “decoy” message from the duck, Eriksson began to tinker with other variables. Taking the duck’s mockery as a literal clue, Eriksson decided to run it through a decryption program called OutGuess. Success: another hidden message, this time linking to another message board on the massively popular news forum Reddit. Here, encrypted lines from a book were being posted every few hours. But there were also strange symbols comprising of several lines and dots – Mayan numbers, Eriksson realized. And duly translated, they led to another cipher.
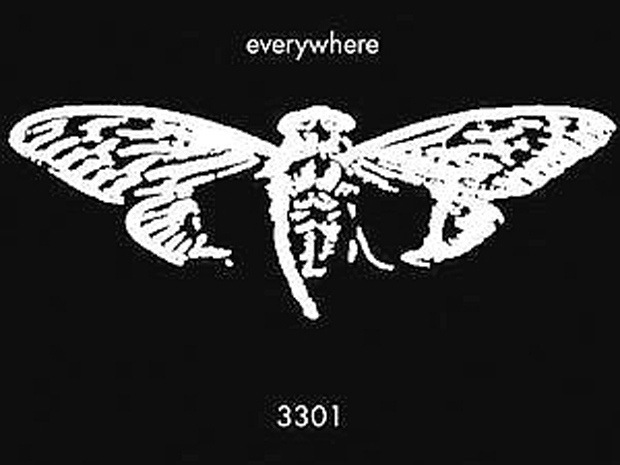
Suddenly, the encryption techniques jumped up a gear. And the puzzles themselves mutated in several different directions: hexadecimal characters, reverse-engineering, prime numbers. Pictures of the cicada insect – reminiscent of the moth imagery in Thomas Harris’s The Silence of the Lambs – became a common motif.
“I knew cicadas only emerge every prime number of years – 13, or 17 – to avoid synchronizing with the life cycles of their predators,” says Eriksson. “It was all starting to fit together.” The references became more arcane too. The book, for example, turned out to be “The Lady of the Fountain”, a poem about King Arthur taken from The Mabinogion, a collection of pre-Christian medieval Welsh manuscripts.
Later, the puzzle would lead him to the cyberpunk writer William Gibson – specifically his 1992 poem “Agrippa” (a book of the dead), infamous for the fact that it was only published on a 3.5in floppy disk, and was programmed to erase itself after being read once. But as word spread across the web, thousands of amateur codebreakers joined the hunt for clues. Armies of users of 4chan, the anarchic internet forum where the first Cicada message is thought to have appeared, pooled their collective intelligence – and endless free time – to crack the puzzles.
‘This was definitely an unexpected turn’
Within hours they’d decoded “The Lady of the Fountain”. The new message, however, was another surprise: “Call us,” it read, “at telephone number 214-390-9608?. By this point, only a few days after the original image was posted, Eriksson had taken time off work to join the pursuit full time.
“This was definitely an unexpected turn,” he recalls. “And the first hint that this might not just be the work of a random internet troll.” Although now disconnected, the phone line was based in Texas, and led to an answering machine. There, a robotic voice told them to find the prime numbers in the original image. By multiplying them together, the solvers found a new prime and a new website: 845145127.com. A countdown clock and a huge picture of a cicada confirmed they were on the right path.

After a designated number of solvers visited the address, the website shut down with a terse message: “We want the best, not the followers.” The chosen few received personal emails – detailing what, none have said, although one solver heard they were now being asked to solve puzzles in private. Eriksson, however, was not among them. “It was my biggest anticlimax – when I was too late to register my email at the TOR hidden service,” he says. “If my sleep-wake cycle had been different, I believe I would have been among the first.” Regardless, a few weeks later, a new message from Cicada was posted on Reddit. It read: “Hello. We have now found the individuals we sought. Thus our month-long journey ends. For now.” All too abruptly for thousands of intrigued solvers, it had gone quiet.
Except no. On January 4 this year, something new. A fresh image, with a new message in the same white text: “Hello again. Our search for intelligent individuals now continues.” Analysis of the image would reveal another poem – this time from the book Liber Al Vel Legis, a religious doctrine by the English occultist and magician Aleister Crowley. From there, the solvers downloaded a 130Mb file containing thousands of prime numbers. And also an MP3 file: a song called The Instar Emergence by the artist 3301, which begins with the sound of – guess what – cicadas.
Analysis of that has since lead to a Twitter account pumping out random numbers, which in turn produced a “gematria”: an ancient Hebrew code table, but this time based on Anglo-Saxon runes. This pointed the solvers back into the darknet, where they found seven new physical locations, from Dallas to Moscow to Okinawa, and more clues. But that’s where, once again, the trail has gone cold. Another select group of “first solvers” have been accepted into a new “private” puzzle – this time, say reports, a kind of Myers-Briggs multiple-choice personality test.
But still, we are no closer to knowing the source, or fundamental purpose, of Cicada 3301. “That’s the beauty of it though,” says Eriksson. “It is impossible to know for sure until you have solved it all.” That is why for him, and thousands of other hooked enthusiasts, January 4 2014 is so important: that’s when the next set of riddles is due to begin again. “Maybe all will be revealed then,” he grins. “But somehow, I doubt it.”
The Sunday Telegraph

![20131203-181937[1]](https://coolinterestingnews.com/wp-content/uploads/2013/12/20131203-1819371.jpg)